- What is Security?
- Before You Begin
- 1. Set Strong and Unique Passwords
- 2. Install SSL
- 3. Security Themes
- 4. Logging
- 5. Monitoring
- 6. File Permissions
- 7. Disable File Editor
- 8. Securing wp-admin
- 9. Securing wp-includes
- 10. Securing wp-config.php file
- 11. Database Security
- 12. Security Through Obscurity
- 13. Using a WordPress security plugin
- 14. Data Backups
- 15. Vulnerabilities on Your Computer
- 16. Vulnerabilities in WordPress
- 17. Web Server Vulnerabilities
- 18. Network Vulnerabilities
- 19. Use FTP
- Conclusion
In the digital age, securing your WordPress website is of utmost importance. Millions of websites rely on WordPress daily, but like any platform, it can be vulnerable to security issues if not properly protected. Even though WordPress developers are consistently working to patch vulnerabilities, website owners must take the necessary precautions to secure their sites.
This article aims to guide you through hardening WordPress security, discussing common vulnerabilities and providing practical steps to address them. However, this article won’t solve all of your security concerns. Website security is an ongoing process, not a one-time task.
It’s recommended to consult with a cybersecurity professional for issues beyond your expertise. At Reliqus Consulting, we specialize in securing WordPress websites and aim to help you understand, implement, and maintain your site’s security measures.
We encourage you to read to learn how to harden your WordPress security.
What is Security?

Security isn’t about having a perfectly secure system but about risk mitigation and applying suitable controls. It entails minimizing risk, not eliminating it. With proper security measures, you can avoid data breaches and site compromises.
Hence, understanding and implementing WordPress hardening and other security best practices is critical.
Website Hosts
Your hosting environment plays a crucial role in your website’s security. The division of responsibility between web hosts and website owners for security is clear: website owners must secure their WordPress installations, while hosts must secure the hosting environment.
A secure server safeguards privacy and integrity while ensuring resource availability. Choosing a trusted web host offering up-to-date software, backups, and recovery methods is essential.
Website Applications
As a website owner, you are responsible for your site’s security. While web hosts safeguard the infrastructure, they don’t handle application security—that’s on you.
Remember, most hacks happen due to application vulnerabilities, not infrastructure issues. Thus, securing your WordPress site is crucial for risk mitigation.
Therefore, securing your WordPress site’s application is crucial to mitigating risk and protecting your online presence from potential threats.
Before You Begin
Our list has been arranged according to ease of implementation, so you can start at the top and work your way down. Opting for professional assistance should be your initial step.
Remember the golden rule: always backup your website before making any changes, even those related to security.
1. Set Strong and Unique Passwords
The core foundation of good security habits is establishing a strong, uncrackable password. Use automatic password generators to create strong and unique passwords that are difficult for hackers to guess.
WordPress has an inbuilt password strength meter to help ensure your password is strong enough.
Avoid using personal information in your password; use a complex combination of letters, numbers, and special characters. Enable two-step authentication for added security. This ensures that even someone with your password cannot log in without access to your personal device.
2. Install SSL

SSL (Secure Socket Layer) is a protocol that transmits data securely over an encrypted connection. Google mandates SSL for websites and imposes penalties on those lacking it.
Previously, installing an SSL certificate was complicated, but it has become simpler. Check out this guide on [how to install an SSL certificate] and ensure all your pages are HTTPS.
3. Security Themes
To enhance your WordPress security, there are several key themes to consider:
– Limit Access: Minimize possible entry points for hackers by restricting access to critical components of your site. Limit who has admin privileges, and employ strong usernames and passwords.
– Containment: A compromise can still occur even with robust security measures. Implement containment strategies to ensure that the breach doesn’t extend to the entire network if one part of your system is compromised.
– Preparation and Knowledge: Stay informed about the latest security threats and best practices. Regularly backup your website and have a disaster recovery plan in place.
– Trusted Sources: Be cautious of where you get your plugins and themes. Stick to trusted sources like the WordPress.org repository or well-known, reputable companies. Plugins and themes from untrusted sources may contain malware, posing significant security risks.
4. Logging
Understanding your website’s activity is vital for security, and logs offer a goldmine of information. They track IP addresses and user actions, aiding in identifying attacks such as Cross-Site Scripting (XSS), Remote File Inclusion (RFI), Local File Inclusion (LFI), and brute force attempts.
Regular examination can reveal theme and plugin usage, widget updates, and content changes. WordPress Security plugins like the Sucuri Auditing tool or the Audit Trail plugin.
Open-source solutions like OSSEC, compatible with NIX distributions and Windows, are crucial for capturing and filtering server logs, provided they’re correctly configured.
5. Monitoring
While preventive measures are a significant aspect of WordPress security, they may not always be enough. Therefore, the role of robust intrusion detection and monitoring becomes crucial.
Monitoring your logs
If you have root access on a dedicated or virtual private server, monitoring your logs can be accomplished with tools like OSSEC. Designed specifically for log monitoring, OSSEC is a user-friendly, reliable, and cost-effective tool used by many.
Monitoring your files for changes
Cyberattacks inevitably leave traces in logs or the file system. OSSEC, a versatile tool previously mentioned, is excellent for monitoring files for changes. It diligently alerts users when files are tampered with, or new ones are created, further bolstering your WordPress site’s security.
Monitoring your web server externally
External monitoring of your web server is crucial to counter attackers who may deface your site or add malware. A web-based integrity monitor solution can detect unauthorized changes made by attackers. Also, consider employing a search engine to find a reputable service provider for web malware detection and remediation.
6. File Permissions
Certain WordPress functionalities require writable files by the web server. However, giving write access to files can be risky, especially on shared hosting.
To maintain a secure environment, tighten file permissions and only loosen them when necessary. Create designated folders with fewer restrictions for activities like file uploads.
A good permission scheme is having all files owned and writable by the user account, while files requiring WordPress write access are group-owned by the web server user account, depending on your hosting setup. Always remember to set permissions for the root directory.
/
The root WordPress directory should have all files writable only by the user account, except the .htaccess if you wish to employ automatic rewrite rules.
/wp-admin/
The WordPress administration area: all files should be writable only by your user account.
/wp-includes/
The bulk of WordPress application logic: all files should be writable only by your user account.
/wp-content/
User-supplied content: intended to be writable by your user account and the web server process.
Within /wp-content/ you will find:
/wp-content/themes/
Theme files. If you want to use the built-in theme editor, all files need to be writable by the web server process. If you do not want to use the built-in theme editor, all files can be writable only by your user account.
/wp-content/plugins/
Plugin files: all files should be writable only by your user account.
Other directories that may be present with /wp-content/ should be documented by whichever plugin or theme requires them. Permissions may vary.
Changing file permissions
Changing file permissions requires shell access to your server and can be executed recursively with the following command:
For Directories:
find /path/to/your/wordpress/install/ -type d -exec chmod 755 {} \;
For Files:
find /path/to/your/wordpress/install/ -type f -exec chmod 644 {} \;
Regarding Automatic Updates
During automatic updates, WordPress conducts all file operations as the owner of the files, not the web server’s user.
This process sets all files to 0644 and directories to 0755, ensuring that only the file owner has write permissions while everyone else, including the web server, can only read them. This enhances the security of your WordPress site by limiting potential unauthorized write access.
7. Disable File Editor
The WordPress Dashboard enables administrators to edit PHP files, such as plugin and theme files, presenting a potential gateway for malicious code execution. WordPress offers a constant that disables editing from the Dashboard.
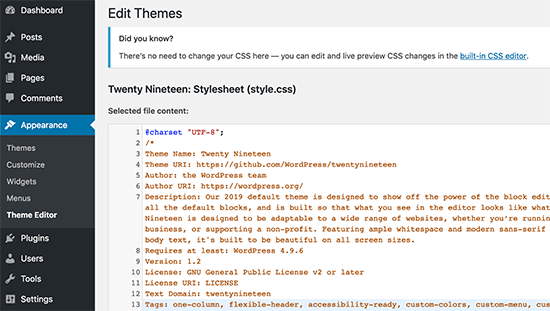
You can activate this by adding it to your wp-config.php. This action essentially removes the ‘edit_themes,’ ‘edit_plugins’ and ‘edit_files’ capabilities of all users:
define( ‘DISALLOW_FILE_EDIT’, true );
While this won’t prevent hackers from uploading malicious files, it’s important to note that it may deter some attacks.
8. Securing wp-admin
Adding server-side password protection (such as BasicAuth) to your wp-admin/ directory provides an additional layer of security, forcing potential attackers to bypass this before reaching your admin files.
However, remember that this could interfere with some WordPress functions, like the AJAX handler at wp-admin/admin-ajax.php.
Most attacks on WordPress blogs come from malicious software bots sending crafted HTTP requests or employing “brute-force” password guessing. An optimal way to secure wp-admin is by requiring an HTTPS SSL encrypted connection for administration, ensuring all data and communication are encrypted.
9. Securing wp-includes
Adding a second layer of protection to scripts not intended for user access provides extra security. Utilize mod_rewrite in the .htaccess file to block these scripts.
Note: It’s essential to place the code mentioned below outside of the # BEGIN WordPress and # END WordPress tags to prevent WordPress from overwriting it.
# Block the include-only files.
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteBase /
RewriteRule ^wp-admin/includes/ – [F,L]
RewriteRule !^wp-includes/ – [S=3]
RewriteRule ^wp-includes/[^/]+\.php$ – [F,L]
RewriteRule ^wp-includes/js/tinymce/langs/.+\.php – [F,L]
RewriteRule ^wp-includes/theme-compat/ – [F,L]
</IfModule>
# BEGIN WordPress
However, this method might not work well with Multisite. The ‘RewriteRule ^wp-includes/[^/]+\.php$ – [F,L]’ line prevents the ms-files.php from generating images. Omitting this line could make your code work with Multisite but potentially reduce security.
10. Securing wp-config.php file
The wp-config.php file, crucial to your WordPress installation, can be moved one directory level up for increased security. This approach places your wp-config.php outside the web-root folder, safeguarding it from potential threats.
Note: Yet, this practice is debated; some argue that moving wp-config.php offers minimal security benefits and, if mismanaged, may even create vulnerabilities. Others refute these assertions.
If you choose this route, place wp-config.php where wp-includes resides. Ensure only you and the web server can read this file by setting a 400 or 440 permission.
For those running a server with .htaccess, consider adding the line “Deny from all” at the top of your file. This will deny access to anyone trying to locate your wp-config.php file, adding an extra layer to your WordPress security.
<files wp-config.php>
order allow,deny
deny from all
</files>
11. Database Security
Maintaining each blog in separate databases managed by distinct users, especially during initial WordPress installation, heightens security by containing potential breaches.
If a hacker infiltrates one blog, accessing others becomes more challenging. If self-administering, understand your MySQL configuration to disable unneeded features, enhancing your site’s defenses.
Restricting Database User Privileges
For regular WordPress operations, the MySQL database user only requires SELECT, INSERT, UPDATE, and DELETE privileges for data read and write purposes. Revoking other database structures and administration privileges such as DROP, ALTER, and GRANT is advisable. This helps improve containment policies and reduce the risk of malicious activities in the event of a security breach.
Note: Certain WordPress updates, plugins, and themes may necessitate structural changes to your database, such as adding new tables or altering the schema. Before these modifications, the database user will need temporary increased privileges to allow successful implementation.
WARNING: Initiating updates without these privileges is risky and Not recommended. Before revoking privileges for security purposes, establish a reliable backup plan. Regularly backup your entire database, verify its success, and confirm the easy restoration. If a database upgrade fails, recover the database to its previous state, grant appropriate permissions, and retry the WordPress update. Remember, most updates won’t change the schema, but significant upgrades may. Regardless of upgrade type, consistent backups are crucial.
12. Security Through Obscurity
While “security through obscurity” is often insufficient, it can complement WordPress security.
- Renaming the administrative account from easily guessed terms like “admin” or “webmaster” can deter brute-force attacks. You can rename the existing account using the MySQL command-like:
UPDATE wp_users SET user_login = ‘newuser’ WHERE user_login = ‘admin’;
or a frontend like phpMyAdmin.
- Changing the table_prefix can also thwart some SQL injection attacks, as many published WordPress-specific attacks assume the default table_prefix is wp_. This method could be better, but it adds an extra layer of security to your WordPress site.
13. Using a WordPress security plugin
Keeping your plugins updated is crucial for WordPress security. Updates often include patches for vulnerabilities, which can help prevent attacks on your site. Additionally, any unused plugins should be deleted from your system. These can provide a potential entry point for hackers, especially if they need to be regularly updated.
a] Firewall
A wide array of plugins and services function as a website firewall. Some of them, Such as iThemes Security or All in One WP Security, work by altering the .htaccess file to restrict access at the Apache level.
Some, such as WordFence and Shield, operate at the WordPress level, providing another layer of protection.
A more robust security solution is to install a Web Application Firewall (WAF), such as ModSecurity, at the web server level.
Companies like Cloudflare, Sucuri, and Incapsula offer website firewalls that act as intermediaries between internet traffic and your hosting server, serving as reverse proxies and functioning as Content Distribution Networks (CDNs).
b] Plugins that need write access
Some plugins may necessitate write access to certain WordPress files and directories. Before granting this access, it is essential to review the plugin’s code or consult a reliable source to verify its authenticity.
c] Code execution plugins
Hardening WordPress is crucial to contain potential damage in case of a successful cyber attack. Plugins allowing arbitrary code execution from database entries significantly increase this potential risk.
Instead, consider using custom page templates, a more secure method, particularly when file editing is disallowed in WordPress. This approach reduces vulnerability to harmful attacks while maintaining your site’s functionality.
14. Data Backups
Regular data backups, including your MySQL databases, are fundamental to WordPress security. Maintaining data integrity in these backups ensures trusted data restoration. Enhance data security by encrypting backups, keeping independent records of MD5 hashes, or utilizing read-only media.
Implement a sound backup strategy, such as regular snapshots of your WordPress installation. For example, a weekly snapshot could be invaluable if your site is compromised. Additionally, post-compromise backups can be analyzed to identify how the breach occurred.
15. Vulnerabilities on Your Computer
Ensure your computer is free from spyware, malware, and viruses. Despite robust site security, keyloggers can still threaten your system. Regularly update your operating system, software, and, particularly, your web browser to safeguard against security vulnerabilities.
To enhance protection, use tools like no-script or disable javascript, flash, and Java when browsing untrusted sites.
16. Vulnerabilities in WordPress
WordPress continuously rolls out updates to address security concerns. Improving software security is always an ongoing concern. However, Older versions of WordPress are not maintained with security updates, making it crucial to keep your WordPress version up to date.
Updating WordPress
The latest WordPress version can always be found at https://wordpress.org. Never download or install WordPress from any other site.
From version 3.7, WordPress has featured automatic updates—use this to simplify updating. Stay informed about updates using the WordPress Dashboard. Read entries on the Dashboard or the WordPress Developer Blog for crucial update steps and security practices.
Remember, if a vulnerability is identified and a new version is released, exploit information might become public—keeping WordPress updated helps prevent potential attacks. If managing multiple WordPress installations, consider using Subversion for easier management.
Reporting Security Issues
If you identify a security flaw in WordPress, it’s imperative to report it. Refer to the Security FAQ on the WordPress website for instructions on reporting security issues.
Additionally, report any bugs you find, as they could potentially lead to vulnerabilities. For guidelines on submitting bugs, visit the website.
17. Web Server Vulnerabilities
The web server running your WordPress site can be a weak link if not properly managed. Use secure and stable server software versions or a trusted hosting provider.
Beware of shared server risks; if one site is compromised, others may be too. Inquire about your host’s security precautions to prevent potential vulnerabilities.
18. Network Vulnerabilities
Secure both your WordPress server and client network. Update firewall rules on your home router and be wary when accessing your site from certain networks, especially unencrypted connections like those in internet cafes.
Your web host should also maintain a secure network. Network vulnerabilities can lead to the interception of sensitive data, so diligent security practices on all networks involved in your WordPress operation are essential.
19. Use FTP
FTP, or File Transfer Protocol, moves files between your computer and your website’s server. Use SFTP, or Secure File Transfer Protocol, if your web host provides it for added security.
SFTP is identical to FTP but adds an extra layer of security through encrypted data transmission. This means attackers cannot intercept passwords and sensitive information.
Conclusion
In conclusion, hardening WordPress security is vital to owning a website. Implementing a WordPress security plugin is crucial, but this can be costly and require technical knowledge.
However, the potential consequences of not securing your website, such as the difficulty of removing malware, can be far more expensive and detrimental to your business. If you need more time to get comfortable with the technical aspects of securing a WordPress website, consider outsourcing to a full-service agency that specializes in WordPress web design and development.
Reliqus Consulting offers comprehensive WordPress hardening and maintenance services, including WordPress software updates, backups, security plugin installation and configuration, server hardening, and regular website maintenance. Partnering with us will ensure your website is properly secured and maintained, allowing you to focus on your business.

